c29c64262b3ee61eaa3b42ae4b7296f7f69d7e20d47e9fb0657508c944e8d910 (SHA-256)
Malicious with 98% Confidence
SecondWrite’s DeepView Sandbox analyzed this file last week and declared it to be malicious.
DeepView unique and patented methods – specifically in this case, force code execution and program level indication – identified 13 indicators. At the time of detection, all the magic quadrant vendors had not identified this file of malicious. A link to the full report with descriptions and details is below.
Some key highlights and indicators follow. Those discovered by DeepView proprietary methods are flagged with [FCE] for forced code execution.
Type of Malware: Adware
- [FCE] Attempts to modify Internet Explorer’s start page
- [FCE] Attempts to create or modify system certificates
- [FCE] Internet Explorer creates one or more Martian processes
- [FCE] Attempts to create or modify system certificates
- [FCE] Sample writes a large amount of files (over 100)
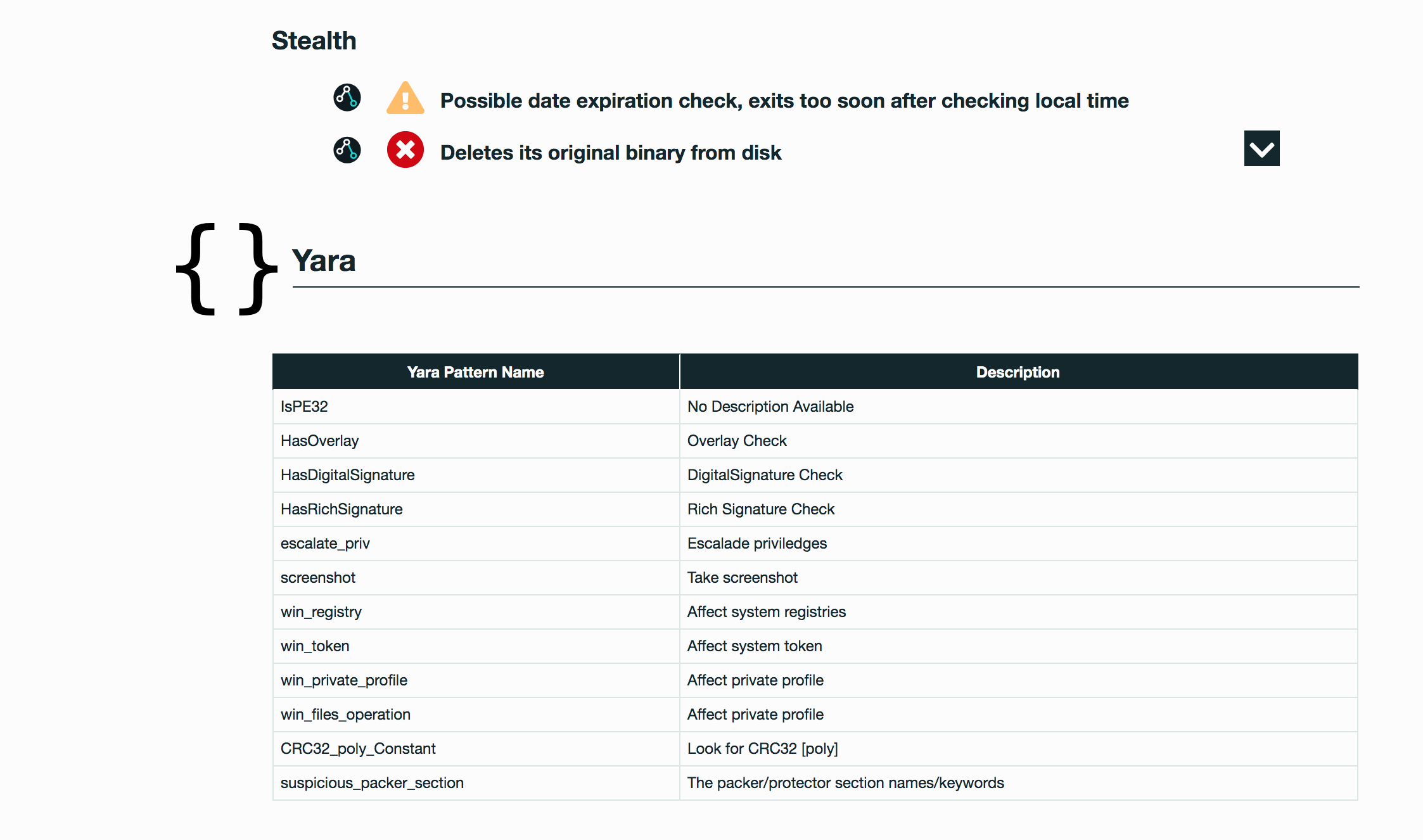
Evasiveness Indicators:
- Checks whether any human activity is being performed by constantly checking whether the foreground window changed
- A process attempted to delay the analysis task
- Attempts to repeatedly call a single API many times in order to delay analysis time
- Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available
- Checks adapter addresses which can be used to detect virtual network interfaces
Other Compelling Indicators:
- Created a service where a service was also not started
- Deletes its original binary from disk
- Creates a suspicious process
MITRE ATT&CK Indicators:
| MITRE Tactic | MITRE Technique |
| Command and Control | Connection Proxy |
| Credential Access | Credential Dumping |
| Defense Evasion | File Deletion NTFS File Attributes Software Packing |
| Discovery | Process Discovery Virtualization / Sandbox Evasion |
Selection from The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.