fb3439936c8be4798abbeb7e4078aef7fa58d6da5d4ffc88c08c14e514f43b94 (SHA-256)
Malicious with 81% Confidence
SecondWrite’s DeepView Sandbox analyzed this file last week and declared it to be malicious using our proprietary techniques. At the time of detection, this malware did not appear on leading malware black lists. A link to the full report is below and some key highlights follow:
Type of Malware: Ransomware
– This sample modifies many files through suspicious ways, likely a polymorphic virus or a ransomware
– Sniffs keystroke
– Creates known Bifrose files, registry keys and/or mutexes
– Drops a binary and executes it
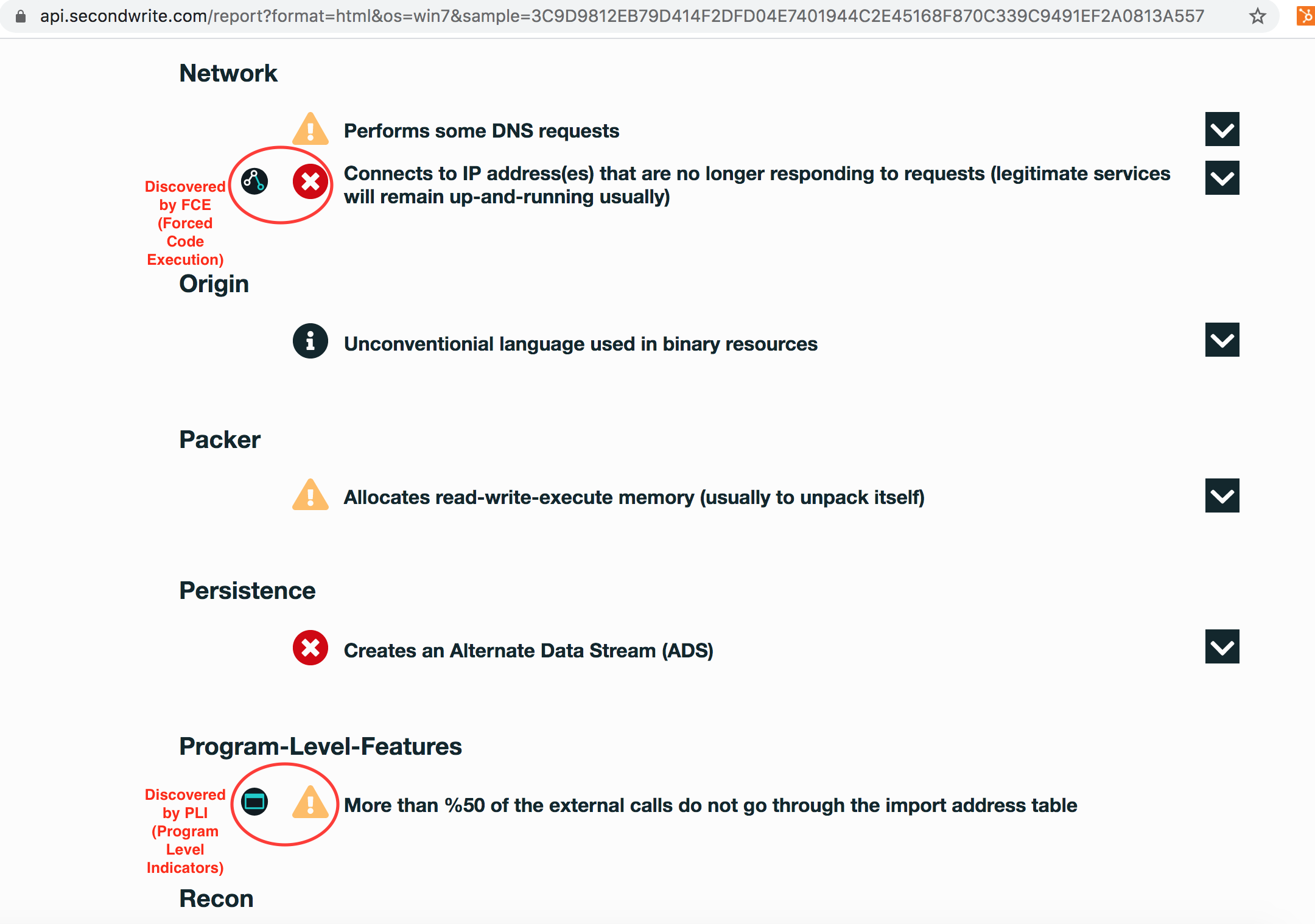
– Performs some DNS requests
Evasiveness Indicators:
– A process attempted to delay the analysis task
– Checks adapter addresses which can be used to detect virtual network interfaces
– Queries for the computername
– Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available
– Allocates read-write-execute memory (usually to unpack itself)
Other Compelling Indicators:
– Deletes its original binary from disk
– Installs itself for autorun at Windows startup
– Attempts to repeatedly call a single API many times in order to delay analysis time
– Creates a service
– The binary likely contains encrypted or compressed data
MITRE ATT&CK Indicators:
– Command and Control
+ Remote File Copy
+ Connection Proxy
– Credential Access
+ Credential Dumping
– Defense Evasion
+ Software Packing
+ File Deletion
– Discovery
+ Process Discovery
+ Virtualization / Sandbox Evasion
Persistence
+ Registry Run Keys / Startup Folder
Selection From The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.