d0092238074d29bd51410e9a48b444d839a2b2f19e424580dba2408c5b1198e9 (SHA-256)
Malicious with 94% Confidence
SecondWrite’s DeepView Sandbox analyzed this file last week and declared it to be malicious.
DeepView unique and patented methods – specifically in this case, force code execution identified 4 indicators. At the time of its discovery, all of the major malware detection vendors had not identified this file of malicious. A link to the full report with descriptions and details is below.
Some key highlights and indicators follow. Those discovered by DeepView proprietary methods are flagged with [FCE] for forced code execution.
Type of Malware: Infostealer
- Steals private information from local Internet browsers
- A process created a hidden window
- Harvests credentials from local FTP client softwares
Evasiveness Indicators:
- A process created a hidden window
- [FCE] Attempts to repeatedly call a single API many times in order to delay analysis time
- A process attempted to delay the analysis task
- [FCE] Tries to suspend Cuckoo threads to prevent logging of malicious activity
- Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available
Other Compelling Indicators:
- [FCE] Checks adapter addresses which can be used to detect virtual network interfaces
- [FCE] Checks the system manufacturer, likely for anti-virtualization
- One or more of the buffers contains an embedded PE file
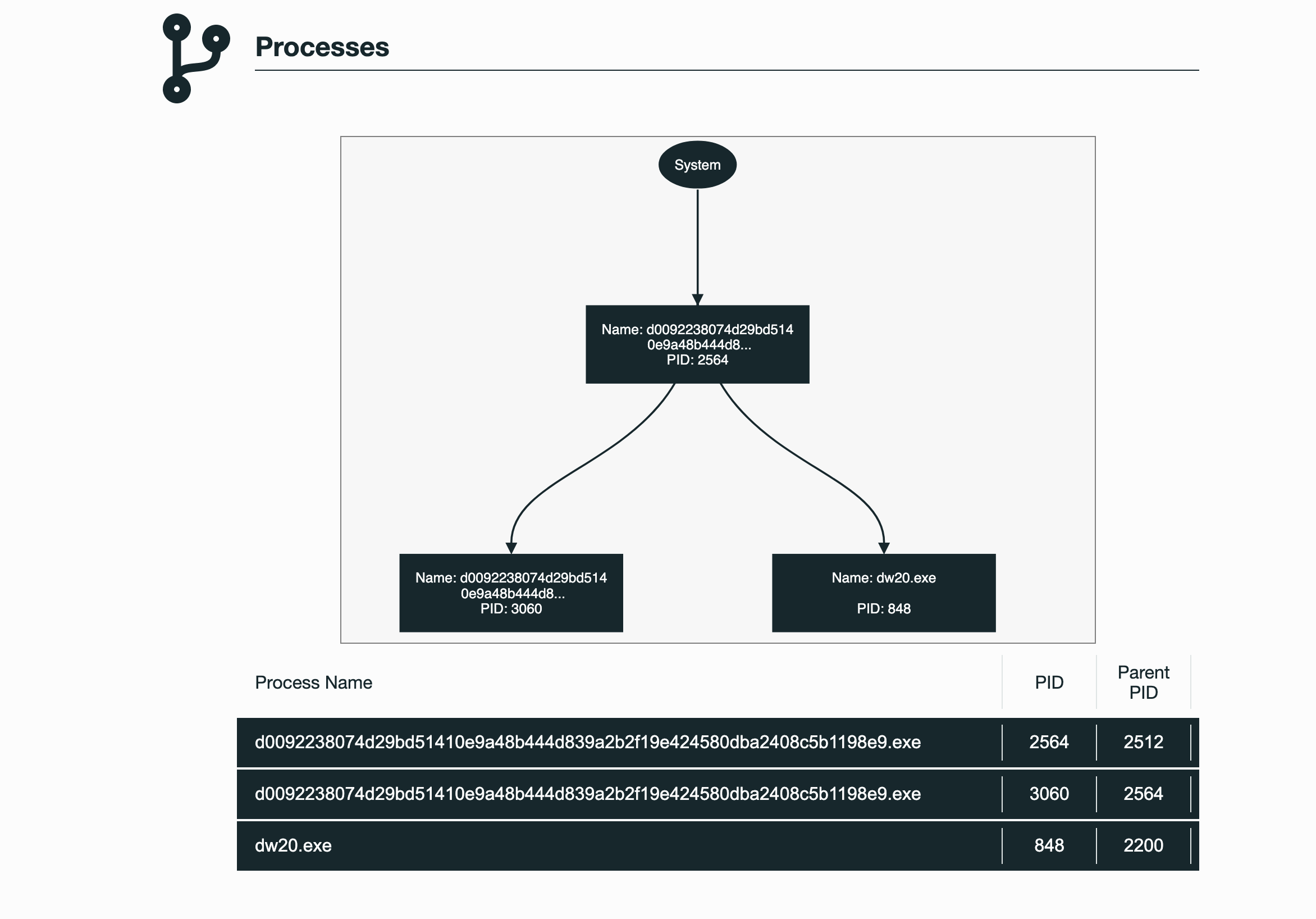
- Executed a process and injected code into it, probably while unpacking
- One or more potentially interesting buffers were extracted, these generally contain injected code, configuration data, etc.
MITRE ATT&CK Indicators:
| MITRE Tactic | MITRE Technique |
| Privilege Escalation | Process Injection |
| Defense Evasion | Virtualization / Sandbox EvasionHidden WindowSoftware PackingProcess Injection |
| Credential Access | Credential Dumping |
| Discovery | Virtualization / Sandbox Evasion |
Selection from The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.
