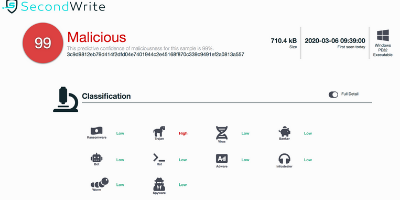
Malicious with 99% Confidence
3C9D9812EB79D414F2DFD04E7401944C2E45168F870C339C9491EF2A0813A557 (SHA-256)
SecondWrite’s DeepView Sandbox analyzed this file last week and declared it to be 99% malicious using our proprietary techniques. A link to the full report is below but here are some key highlights:
Type Of Malware: Trojan
- More than %50 of the external calls do not go through the import address table
- Creates executable files on the filesystem
- Deletes its original binary from disk
Evasiveness Indicators:
- Tries to suspend Cuckoo threads to prevent logging of malicious activity
- Checks the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation
- Checks adapter addresses which can be used to detect virtual network interfaces
- Executes one or more WMI queries which could be used to identify virtual machines
- Attempts to repeatedly call a single API many times in order to delay analysis time
Other Compelling Indicators:
- Drops a binary and executes it
- Attempts to create or modify system certificates
- Attempts to connect to dead IP:Port(s)
- One or more of the buffers contains an embedded PE file
- Connects to IP address(es) that are no longer responding to requests (legitimate services will remain up-and-running usually)
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection
Please email us at info@secondwrite.com to questions about our product
SecondWrite’s malware detection sandbox and threat intelligence products are bringing novel technologies and capabilities to their respective segments for the first time. SecondWrite’s DeepView sandbox product categorizes customer-submitted files as malicious or benign with industry-leading accuracy, and outputs a report detailing the file’s suspicious activity. Unlike competing sandboxes, DeepView forcibly executes hidden malicious paths in the input file, thereby discovering about 50% more Indicators of Compromise (IOCs) than without this technology, and leading to greater detection accuracy.