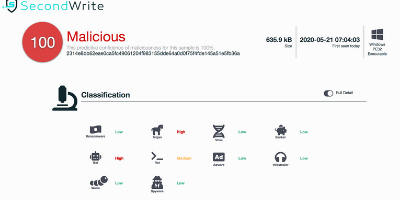
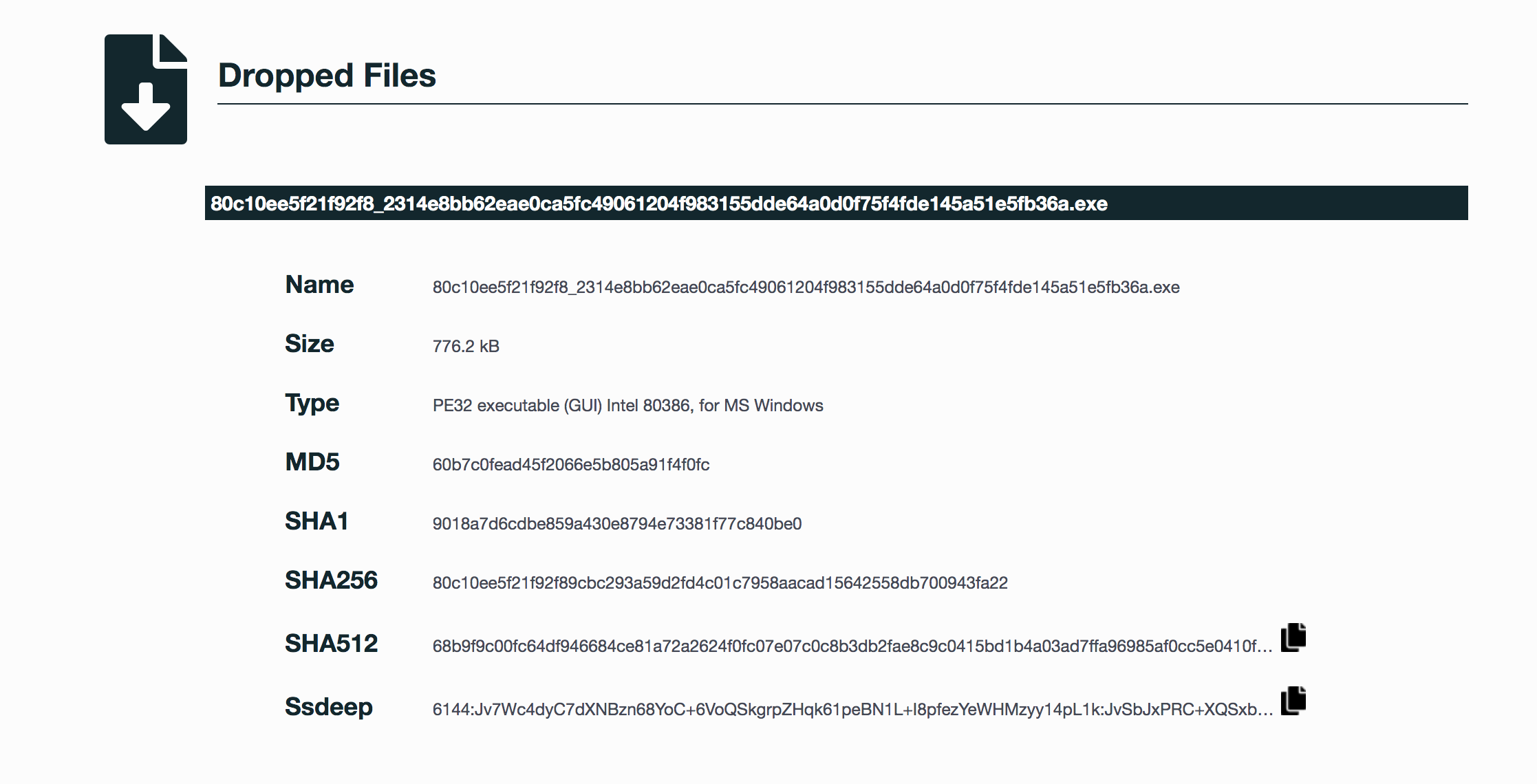
2314e8bb62eae0ca5fc49061204f983155dde64a0d0f75f4fde145a51e5fb36a (SHA-256)
Malicious with 100% Confidence
SecondWrite’s DeepView Sandbox analyzed this file last week and declared it to be malicious using our proprietary techniques – which in this case uncovered 5 indicators of significance. SecondWrite’s DeepView unique, patented methods – specifically in this case, force code execution and program level indication – identified 14 indicators. A link to the full report with descriptions and details is below.
Some key highlights and indicators follow:
Type of Malware: Bot
- Installs itself for autorun at Windows startup
- Creates an Alternate Data Stream (ADS)
- More than %50 of the external calls do not go through the import address table
- Creates a suspicious process
- Unconventional language used in binary resources
Evasiveness Indicators:
- Checks whether any human activity is being performed by constantly checking whether the foreground window changed
- Checks adapter addresses which can be used to detect virtual network interfaces
- Attempts to repeatedly call a single API many times in order to delay analysis time
- Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available
- Detects VMWare through the in-instruction feature
Other Compelling Indicators:
- Creates executable files on the filesystem
- Executes one or more WMI queries
- Performs some HTTP requests
- Attempts to identify installed AV products by registry key
- Strings possibly contain hardcoded IP Addresses
MITRE ATT&CK Indicators:
| MITRE Tactic | MITRE Technique |
| Defense Evasion | Hidden Window NTFS File Attributes |
| Discovery | Process Discovery Security Software Discovery Virtualization / Sandbox Evasion |
| Persistence | Registry Run Keys / Startup Folder |
Selection from The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.