1176637004956c3cde0de41c5dde29ad7be714d07d6426174d89b56b85669f9b (SHA-256)
Malicious with 100% Confidence
SecondWrite’s DeepView Sandbox analyzed this file – a Windows PE32 Executable – this week and declared it to be malicious. At the time of its discovery, all major malware detection vendors had not identified this file as malicious. DeepView unique and patented methods identified 4 indicators – specifically in this case, force code execution (FCE), program level indication (PLI), and automated sequence detection (ASD).
A link to the full report with descriptions and details is below. Some key highlights and indicators follow.
Type of Malware: Ransomware
- Sample writes a large amount of files (Over 100)
- Installs itself for autorun at Windows startup
- Attempts to disable UAC
- Expresses interest in specific running processes
- Attempts to modify Explorer settings to prevent file extensions from being displayed
Evasiveness Indicators:
- [FCE] Attempts to repeatedly call a single API many times in order to delay analysis time
- [PLI] Contains obfuscated control-flow to defeat static analysis
- [PLI] A process attempted to delay the analysis task
- Uses anti-binary translation code by allocating huge blocks
- Disables Windows Security features
Other Compelling Indicators:
- [ASD] Automatic Sequence Detection maliciousness score: 56%
- Expresses interest in specific running processes
- Attempts to modify Explorer settings to prevent hidden files from being displayed
- Allocates read-write-execute memory (usually to unpack itself)
- Creates a service
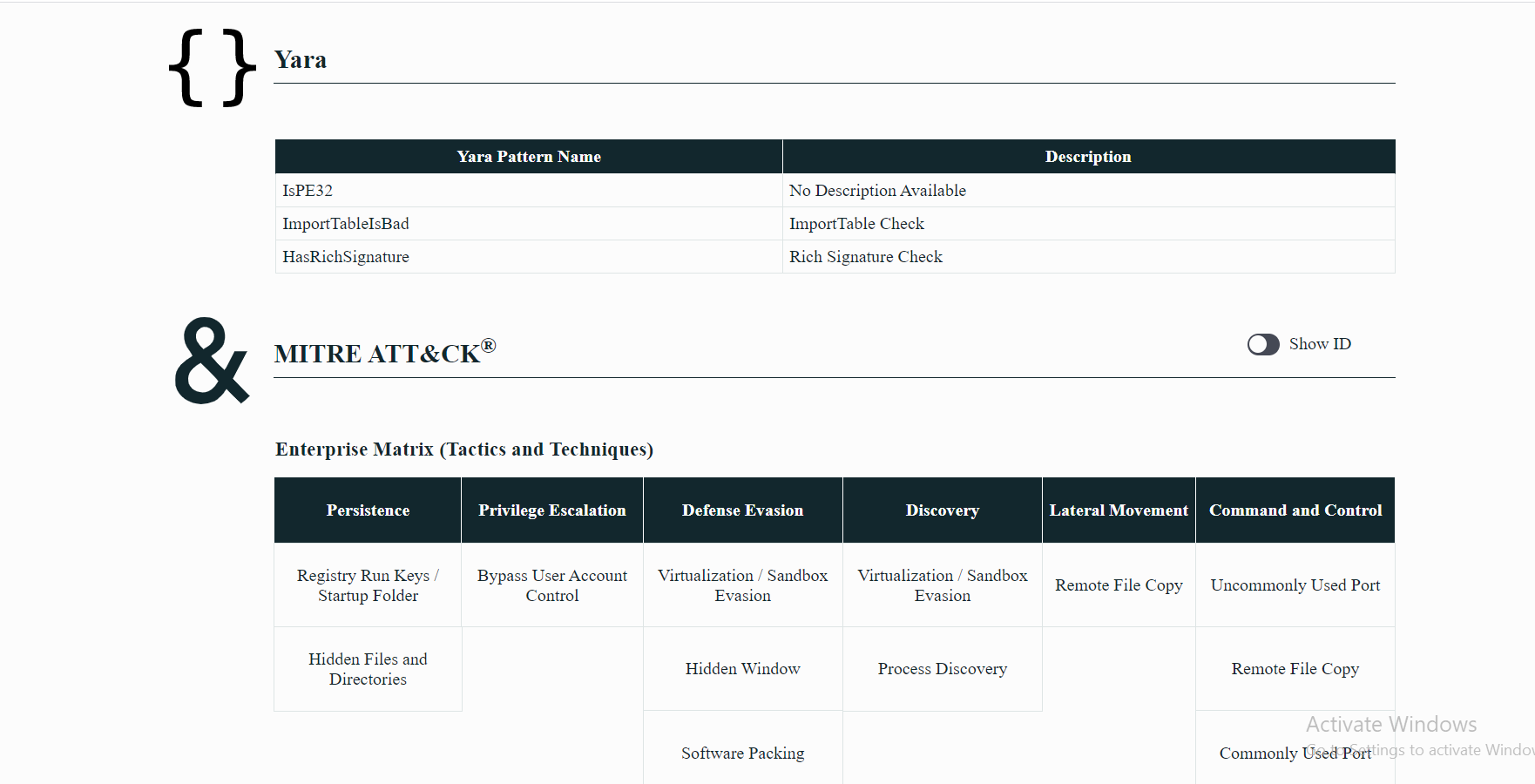
MITRE ATT&CK Indicators:
| MITRE Tactic | MITRE Technique |
| Command and Control | Commonly Used Port Custom Command and Control Protocol Remote File Copy Uncommonly Used Port |
| Defense Evasion | Bypass User Account Control Disabling Security Tools File Deletion Hidden Files and Directories Hidden Window Software Packing |
| Discovery | Process Discovery Virtualization / Sandbox Evasion |
| Persistence | Hidden Files and Directories Registry Run Keys / Startup Folder |
Selection from The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.