7d4d29afaa8b5016c383b43a116283d2c52d13d0dbb23ab9c1e47bcedd8e15dc (SHA-256)
Malicious with 81% Confidence
SecondWrite’s DeepView Sandbox analyzed this file this week and declared it to be malicious. At the time of its discovery, all major malware detection vendors had not identified this file of malicious. DeepView unique and patented methods – specifically in this case, force code execution (FCE), program level indication (PLI), and automatic sequence detection (ASD) – identified 6 indicators. A link to the full report with descriptions and details is below.
Some key highlights and indicators follow. Those discovered by DeepView proprietary method are flagged with [FCE] for forced code execution and [PLI] for program level indication.
Type of Malware: Trojan
- [ASD] More than %50 of the external calls do not go through the import address table
- [FCE] Creates an Alternate Data Stream (ADS)
- Creates executable files on the filesystem
- One or more potentially interesting buffers were extracted, these generally contain injected code, configuration data, etc.
- Attempts to execute a powershell command with suspicious parameter/s
Evasiveness Indicators:
- [FCE] Tries to suspend sandbox threads to prevent logging of malicious activity
- [FCE] Attempts to repeatedly call a single API many times in order to delay analysis time
- Queries for the computername
- Checks amount of memory in system, this can be used to detect virtual machines that have a low amount of memory available
- [FCE] Installs an hook procedure to monitor for mouse events
Other Compelling Indicators:
- Allocates read-write-execute memory (usually to unpack itself)
- [FCE] Sniffs keystrokes
- Creates a hidden or system file
- Reads data out of its own binary image
- Attempts to identify installed AV products by installation directory
MITRE ATT&CK Indicators:
| MITRE Tactic | MITRE Technique |
| Credential Access | Credential Dumping |
| Defense Evasion | Hidden Files and DirectoriesHidden WindowNTFS File AttributesSoftware Packing |
| Discovery | Security Software DiscoveryVirtualization / Sandbox Evasion |
| Execution | Scripting |
| Persistence | Hidden Files and Directories |
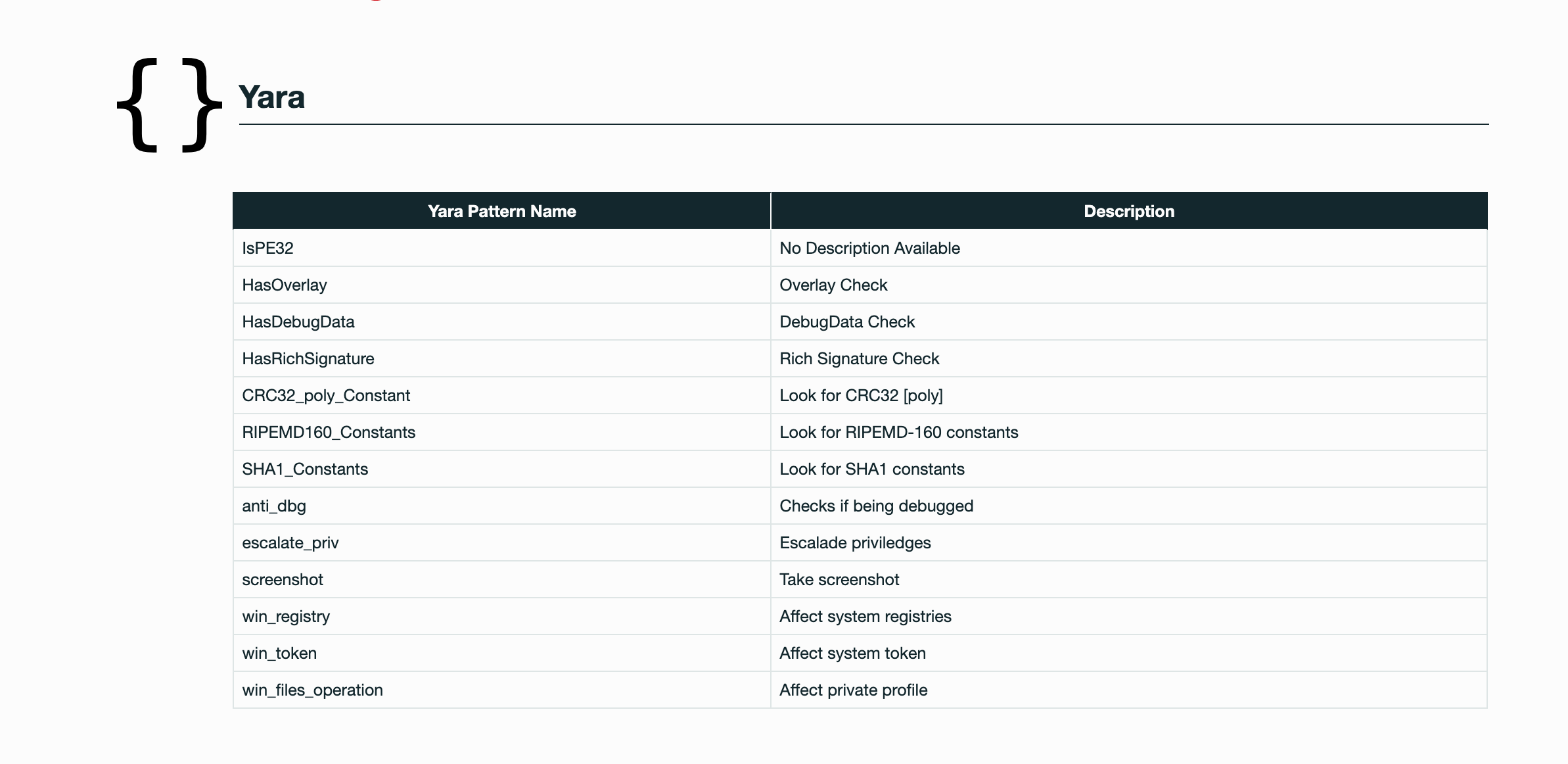
Selection from The Report:
See Full Detailed Report:
Malware Of The Week is sourced by DeepView Sandbox using SecondWrite’s patented techniques of Forced Code Execution, Program Level Indicators, and Automatic Sequence Detection.
