…
Why Dwell Time Matters & What To Do About It
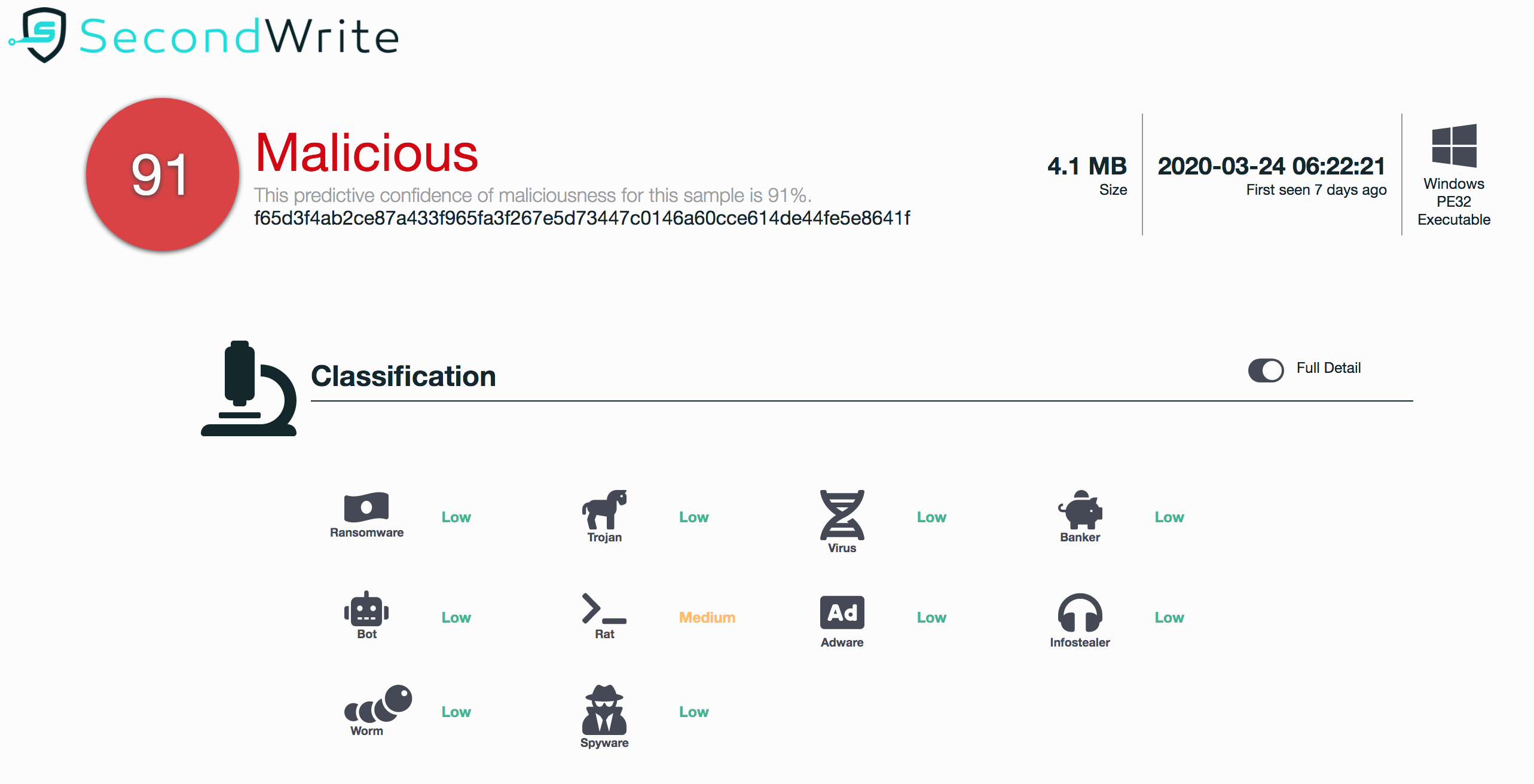
At SecondWrite, we compared the detection results of the three evasive malware samples deemed malicious by our DeepViewTM cloud-based malware detector against other leading endpoint tools from Gartner’s magic quadrant.
EpicNet – Hidden traffic, payload, and persistence
At SecondWrite, we analyzed the EpicNet sample (Malware SHA256 Hash: A2C0B6D31DC39ED651B29729C10E748073001DD4F58F599E5B418954B4ECCA5D) using SecondWrite’s DeepView sandbox
What to do about evasive malware?
Malware reverse engineering is a time consuming and difficult process. Most SOCs don’t employ team members with the time and/or skill set required to focus on a single sample, and so they must rely on external tools or malware
SECONDWRITE’S MALWARE DEEPVIEW CAUGHT WANNA CRY MALWARE WITH NO SIGNATURES
WannaCry, a recent ransomware attack, is impacting organizations worldwide, with losses estimated at $4B in more than 150 countries.